![]()
![]()
![]()
Use LEFT and RIGHT arrow keys to navigate between flashcards;
Use UP and DOWN arrow keys to flip the card;
H to show hint;
A reads text to speech;
490 Cards in this Set
- Front
- Back
|
Each of the following is a layer that protects information security except.
A. products B. people C. communication D. procedures |
Communication
|
|
|
Each of the following is a reason why security is becoming increasingly difficult except.
A. speed of attacks B. slower processors C. sophistication of attacks D. faster detection of weaknesses |
Slower processors
|
|
|
_____ is a category of attacker who only wants to expose security flaws
A. Hacker B. Cracker C. Employee D. Spy |
Hacker
|
|
|
Guarding the availability of information is achieved by.
A. access control B. closed system authentication C. wireless protection environment (WPE) D. frame count check (FCC) |
access control
|
|
|
_____ is the science of transforming information so that it is secure while it is being transmitted or stored.
A. Default key transformation (DRT) B. Access control C.Steganography D. Cryptolography |
Cryptography
|
|
|
Cryptography depends upon the process called an algorithm that uses a cipher.
True or False |
True
|
|
|
Using the same (shared) secret key to both encrypt as well as decrypt is called private key cryptography or symmetric encryption algorithms.
True or False |
True
|
|
|
WEP keys must be a minimum of 1,664 bits in length.
True or False |
False, 40 bit or 140 bit
|
|
|
WEP can support up to 32 keys, but only one of which can be the default key.
True or False |
False, can support only 4 keys
|
|
|
The initialization vector (IV) is a 24-bit value that changes each time a packet is encrypted.
True or False |
True
|
|
|
The output of the pseudo-random number generator (PRNG) is the _____ _____.
|
Key Stream
|
|
|
The _____ is added to the front ("pre-pended") of the ciphertext and is plaintext and is not encrypted
|
Initialization Vector (IV)
|
|
|
RC4 is a stream _____ that accepts keys up to 128 bits in length and takes one character and replaces it with one character.
|
cipher
|
|
|
In order for an attacker to be authenticated he only has to discover the _____.
|
SSID
|
|
|
In a(n) _____ attack and attacker attempts to create every possible key combination by systematically changing one character at a time in possible default key, and then using each newly generated key to decrypt a message.
|
brute force
|
|
|
Restricting access to authorized users.
|
Access Control
|
|
|
The underlying process or formula for encrypting and decrypting messages.
|
algorithm
|
|
|
An attack in which an attacker attempts to create every possible key combination by systematically changing one character at a time in a possible key.
|
brute force attack
|
|
|
An encryption algorithm
|
cipher
|
|
|
An encrypted message
|
ciphertext
|
|
|
In wireless security, two packets that were created from the same initialization vector (IV)
|
collision
|
|
|
A person who has been hired to break into a computer and steal information.
|
computer spy
|
|
|
A person who violates system security with malicious intent.
|
cracker
|
|
|
The science of transforming information so that it is secure while it is being transmitted or stored.
|
cryptography
|
|
|
Terrorists who attack networks and computer infrastructures in order to cause panic.
|
cyberterrorists
|
|
|
A checksum value that is based on the contents of the text.
|
cyclic redundancy check (CRC)
|
|
|
An attack that takes advantage of a previously unknown flaw.
|
day zero attack
|
|
|
The process of changing a ciphertext into plaintext
|
decryption
|
|
|
A key value that is used to encrypt wireless data transmissions when they are sent.
|
default key
|
|
|
An attack that attempts to make a server or other network device unavailable by flooding it with requests.
|
denial of service (DoS) attack
|
|
|
The process of changing plaintext into ciphertext.
|
encryption
|
|
|
Restricting access to authorized users.
|
filtering
|
|
|
A person who uses his or her advanced computer skills to attack computers but not with a malicious intent.
|
Hacker
|
|
|
Protecting the confidentiality, integrity, and availability of information on the devices that store, manipulate, and transmit the information through products, people, and procedures.
|
Information Security
|
|
|
A 24-bit WEP value that changes each time a packet is encrypted.
|
Initialization Vector (IV)
|
|
|
The checksum value generated by WEP.
|
Integrity Check Value (ICV)
|
|
|
An attack technique that floods the radio frequency spectrum with noise.
|
jamming
|
|
|
The value that an algorithm uses to encrypt or decrypt a message.
|
key
|
|
|
The output from a pseudo-random number generator (PRNG).
|
keystream
|
|
|
An attack method to determining the keystream by analyzing two packets that were created from the same initialization vector (IV).
|
keystream attack
|
|
|
An attack that intercepts communication from one device and sends a substitute communication to the intended receiver.
|
man-in-the-middle attack
|
|
|
An access control method that restricts access based on media access control (MAC) address.
|
Media Access Control (MAC) address filtering
|
|
|
A message in an unencrypted format.
|
plaintext
|
|
|
Using the same shared secret key to both encrypt and decrypt messages.
|
Private Key Cryptography
|
|
|
A part of the process for encrypting packages using WEP that generates a keystream.
|
Pseudo-Random Number Generator (PRNG)
|
|
|
A cipher algorithm used in WEP.
|
RC4
|
|
|
Unskilled or novice attackers who break into computers to create damage.
|
Script Kiddies
|
|
|
The process of hiding data so that it cannot be discovered.
|
Steganography
|
|
|
A cipher that takes one character and replaces it with one character.
|
Stream Cipher
|
|
|
Using the same shared secret key to both encrypt and decrypt messages.
|
Symmetric Encryption
|
|
|
A cryptographic key that creates a repeating pattern.
|
Weak Key
|
|
|
AN IEEE 802.11 cryptography mechanism.
|
Wired Equivalent Privacy (WEP)
|
|
|
After the IEEE 802.11 standard was ratified in 1999 independent studies identified WEP weakness by the year ----.
A. 2001 B. 2003 C. 2004 D. 2005 |
2001
|
|
|
The two primary security vulnerabilities of the original 802.11 wireless security mechanism are ____ and _____.
A. Speed and Data Modeling B. Encryption and Authentication C. Access Codes and passwords D. Tokens and Resources |
Encryption and Authentication
|
|
|
WPA and WPA2 were created by which organization.
A. IEEE B. CompTIA C. Wi-Fi Alliance D. Wireless Research Resource Group (WRRG) |
IEEE
|
|
|
After the security flaws in WEP were publicized, the IEEE TGi task group released a new proposed implementation known as _____.
A. WPA B. WEP2 C. TKIP D. Dynamic TKIP |
WEP2
|
|
|
_____ is another name for the IEEE 802.11 standard.
A. Robust Security Network (RSN) B. Wireless Access protection 2 (WAP2) C. Encryption Model II D. Enterprise Standard Security (ESS) |
Robust Security Network (RSN)
|
|
|
Advanced Encryption Standard (AES) is a block cipher.
True Flase |
True
|
|
|
The IEEE 802.1x standard enforces port security.
True False |
True
|
|
|
Pre - authentication allows a device to become authenticated prior to being turned on.
True Flase |
False, the device must be turned on in order for the device to authenticate.
|
|
|
Wi-Fi Protected Access (WPA) is a subset of IEEE 802.11i
True False |
True
|
|
|
MIC performs encryption by using a per-byte key.
True False |
False
|
|
|
The _____ replaces the Cyclic Redundancy Check (CRC) function in WEP
|
MIC
|
|
|
Unlike WEP, the _____ is not used for encryption but instead serves as the starting point (seed) for mathematically generating the encryption keys.
|
Passphrase
|
|
|
_____ allows both AES and TKIP clients to operate in the same WLAN, whereas IEEE 802.11i only recognizes TKIP.
|
WPA2
|
|
|
The _____ security model should only be implemented as a temporary solution.
|
Transition
|
|
|
Shared key authentication uses _____ keys for authentication.
|
WEP
|
|
|
List the three steps that should be taken for the implementing the transitional security model.
|
1. Block Broadcast SSID
2. Shared Key Authentication. 3. MAC Filtering |
|
|
When should the personal security model be implemented.
|
In small office or home environments
|
|
|
Why should AES encryption and decryption be performed in hardware instead of software.
|
It is heavy and really needs an extra on board chip to process the encryption and decryption.
|
|
|
Does a RADIUS server support IEEE 802.1x
|
Yes
|
|
|
What is a virtual private network (VPN)
|
A network that uses a public, unsecured network as if it were a private, secured network.
|
|
|
A block cipher used in IEEE 802.11i
|
Advanced Encryption Standard (AES)
|
|
|
The encryption protocol in the 802.11i standard.
|
AES-CCMP
|
|
|
A server on an IEEE 802.1x network that verifies the authentication of devices.
|
Authentication Server
|
|
|
A device that receives requests in an 802.1x network
|
Authenticator
|
|
|
A cipher that manipulates an entire block of plaintext at one time.
|
Block Cipher
|
|
|
Traffic that is sent to all users on the network.
|
Broadcast
|
|
|
A Web page that wireless users are forced to access prior to being granted access to the wireless network. At a captive portal, users are required to agree to terms of use before being granted access to the network.
|
Captive Portal
|
|
|
A proposed solution to solve the weak initialization vector (IV) problem by rotating the keys frequently.
|
Dynamic WEP
|
|
|
The end of the tunnel between VPN devices.
|
Endpoint
|
|
|
A wireless security model designed for medium to large-size organization such as businesses, government agencies, and universities in which an authentication server is available.
|
Enterprise Security Model
|
|
|
A device that creates a "trusted" VPN connection between itself and another enterprise trusted gateway.
|
Enterprise Trusted Gateway
|
|
|
A protocol that is used on IEEE 802.1x networks.
|
Extensible Authentication Protocol (EAP)
|
|
|
A standard for authentication and key management that can be used for either wired or wireless networks.
|
IEEE 802.1x
|
|
|
A wireless security standard intended to replace the original WEP-based standard.
|
IEEE 802.11i
|
|
|
A security device that monitors network activity instead of filtering packets.
|
Intrusion Detection System (IDS)
|
|
|
A technology developed by the Massachusetts Institute of Technology (MIT) used to verify the identity of network users.
|
Kerberos
|
|
|
A technology that stores information from a device on the network to improve roaming.
|
key-caching
|
|
|
A technology that replaces the Cyclic Redundancy Check (CRC) and is designed to prevent an attacker from capturing, altering, and resending data packets.
|
Message Integrity Check (MIC)
|
|
|
A technology that dynamically generates a new key for each packet and prevents network collisions.
|
per-packet key
|
|
|
A model for wireless security designed for single users or small office home office (SOHO) settings of 10 or fewer wireless devices.
|
Personal Security Model
|
|
|
An authentication technique that blocks all traffic until the user is approved.
|
Port Security
|
|
|
A technology that allows a device to become authenticated to an AP before moving to it.
|
Pre-Authentication
|
|
|
A technology that uses passphrases for generating encryption keys.
|
Pre-Shared Key (PSK)
|
|
|
The interval that PSK keys are changed.
|
Rekey Interval
|
|
|
The process of automatically changing PSK keys are changed.
|
Rekeying
|
|
|
An authentication server typically used on an IEEE 802.1x network.
|
Remote Authentication Dial-In User Service (RADIUS)
|
|
|
A virtual private network which is a user-to-LAN connection used by remote users.
|
Remote-Access VPN
|
|
|
Another name for IEEE 802.11i
|
Robust Security Network (RSN)
|
|
|
A method of setting permissions to a position or role and then assigning users to that role.
|
Role Based Access Control (RBAC)
|
|
|
An iteration in a block cipher.
|
Round
|
|
|
The starting point for mathematically generating an encryption key.
|
Seed
|
|
|
A passphrase in pre-shared key (PSK) authentication that must be entered in both the access point and wireless device.
|
Shared Secret
|
|
|
A virtual private network in which multiple sites can connect to other sites over the Internet.
|
Site-to-Site VPN
|
|
|
A collection of requirements specific to the system or procedure that must be met by everyone.
|
Standard
|
|
|
The wireless device that requires secure network access in an IEEE 802.1x network.
|
Supplicant
|
|
|
A 128-bit encryption key used in TKIP
|
Temporal Key
|
|
|
A technology that replaces WEP encryption.
|
Temporal Key Integrity Protocol (TKIP)
|
|
|
A model for wireless security that should only be implemented as a temporary solution before upgrading to a more secure model, either the personal security model or the enterprise seccurity model.
|
Transitional Security Model
|
|
|
A network that uses a public, unsecured network as if it were a private, secured network.
|
Virtual Private Network (VPN)
|
|
|
A device that aggregates hundreds or thousands of connections together.
|
VPN Concentrator
|
|
|
A proposed standard standard that addresses the limitations of WEP by adding two new security enhancements.
|
WEP2 (WEP Version 2)
|
|
|
A subset of 802.11i that addresses encryption and authentication.
|
Wi-Fi Protected Access (WPA)
|
|
|
The second generation of WPA security , based on the IEEE 802.11i standard.
|
Wi-Fi Protected Access 2 (WPA2)
|
|
|
An access point that is equipped with additional functionality such as a VPN and an authentication server.
|
Wireless Gateway
|
|
|
A device that monitors the RF frequency for attacks.
|
Wireless Intrusion Detection System (WIDS)
|
|
|
A device that performs routing functions by communicating with access points over the RF frequency to determine the most efficient transmission path.
|
Wireless LAN Mesh Router
|
|
|
Hardware device or software that monitors the RF frequency for rogue access points.
|
Wireless Sensor.
|
|
|
Explain how WEP violates the "cardinal rule" of cryptography.
|
Wep creates a detectible pattern
|
|
|
What is a man-in-the-middle attack and how can one be launched against a wireless network.
|
It is when the communication is intercepted and rerouted through a unauthorized source before continuing on to its destination.
|
|
|
List two ways in which a denial service (DoS) attack can be launched against a WLAN.
|
Jamming and Disassociation
|
|
|
Explain how and attacker can force a renegotiation to capture SSID.
|
After causing a dissociation, can send a reassociation frame causing the SSID to be presented.
|
|
|
What is a dictionary attack.
|
An attack that takes each word from a dictionary and encodes it in the same way a passphrase was encoded.
|
|
|
Two perpendicular planes that are used to create a three-dimensional image of RF radiation patterns.
|
Azimuth and Elevation
|
|
|
Practices that establish the benchmark for actions using the network
|
Baseline Practices
|
|
|
An amplifier that boosts the RF signal before it is injected into the device that contains the antenna.
|
Bidirectional Amplifier
|
|
|
Practices that outline the structure and scope of a wireless security plan and how it will be implemented.
|
Design and Implementation Practices
|
|
|
The measure of the antenna gain less the cable loss at the receiver and the receiver's sensitivity.
|
Effective Receiving Sensibility
|
|
|
Nonvolatile storage chip used in computers and other devices that can be programmed and erased multiple times electrically.
|
Electrically-Erasable Programmable Read-Only Memory (EEPROM)
|
|
|
A record of events on the wireless network that is recorded by the access point.
|
Event Log
|
|
|
The difference between the strongest RF signal in an area and the weakest signal that a receiver can process.
|
Fade Margin
|
|
|
Software that is embedded into hardware.
|
Firmware
|
|
|
An attenuator that limits the RF power by a set amount.
|
Fixed-loss Attenuator
|
|
|
A metal rod inserted into the earth for grounding purposes.
|
Ground Rod
|
|
|
The process of determining the likelihood that a vulnerability is a risk to the organization.
|
Impact Analysis
|
|
|
A device that limits the amplitude and disturbing interference voltages by channeling them to the ground.
|
Lightening Arrestor
|
|
|
A rough calculation of all known elements of the link to determine if the signal will have the proper strength when it researches the other end of the link.
|
Link budget
|
|
|
The repository of SNMP data.
|
Management Information Base (MIB)
|
|
|
An antenna that is typically used in outdoor areas.
|
Panel Antenna
|
|
|
The protection of equipment and networking infrastructure itself from unauthorized users from reaching the physical equipment in order to use, steal, or vandalize it.
|
Physical Security
|
|
|
An SNMP-based tool that is used to monitor LANs that are connected through a wide area network.
|
Remote Monitoring (RMON)
|
|
|
A device that amplifies or increases the amplitude of an RF signal.
|
RF amplifier
|
|
|
A device that decreases the RF signal.
|
RF attenuator
|
|
|
Modifying the settings of an access point after a firmware upgrade or simiar modification.
|
RF site tuning
|
|
|
The process of determining the nature of the risks to the organization's assets.
|
Risk Assessment
|
|
|
An antenna for an access point that looks like a slim rod approximately half an inch in diameter and may vary in length from four to six inches
|
Rod Antenna
|
|
|
An antenna that divides the standard 360-degree pattern into four quarters, each with its own transmitter and antenna.
|
Sectorized Antenna
|
|
|
The process of examining the current security of an organization.
|
Security Auditing
|
|
|
A document or series of documents that defines the defense mechanisms an organization will employ to keep information secure.
|
Security Policy
|
|
|
A TCP\IP protocol that allows computers and network equipment to gather data about network performance.
|
Simple Network Management Protocol (SNMP)
|
|
|
A device with the SNMP management software that collects data.
|
SNMP Management Station
|
|
|
An alert message sent to the management station.
|
SNMP trap
|
|
|
An attack that relies on tricking or deceiving someone to access a system.
|
Social Engineering
|
|
|
Software that is loaded onto a network device that will be managed using SNMP.
|
Software Agent
|
|
|
A device that has a single input connector and multiple output connectors.
|
Splitter
|
|
|
The measure of the overall RF level of a system.
|
System Operating Margin (SOM)
|
|
|
An amplifier that increases the RF signal level before it is injected into the transmitting antenna.
|
Unidirectional Amplifier
|
|
|
An attenuator that allows the user to set the amount of loss.
|
Variable-Loss Attenuator
|
|
|
A tool that compares the asset against a database of known vulnerabilites and produces a discovery report that exposes the vulnerability and assesses its severity.
|
Vulnerability Scanner
|
|
|
Collection of methods used to ensure a computer system is secure
|
Computer Security
|
|
|
Collection of methods used to ensure multiple computer systems and devices that are connected together are protected
|
Network Security
|
|
|
Collection of methods used to ensure data stored and processed is secure
|
Information Security
|
|
|
Collection of methods used to ensure data and processing systems are available to authorized subjects upon request
|
Information Assurance
|
|
|
The 'C' in CIA
|
Confidentiality
|
|
|
The 'I' in CIA
|
Integrity
|
|
|
The 'A' in CIA
|
Availability
|
|
|
To ensure that information is accessed only by those whose access is authorized, and never by anybody else
|
Confidentiality
|
|
|
To ensure that information is created, altered, or deleted by authorized people only, and never by anybody else
|
Integrity
|
|
|
To ensure that information and the processing system is available for use by authorized people when they need it
|
Availability
|
|
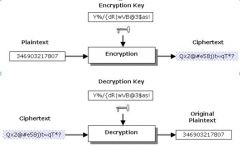
What does the graphic represent
|
Encryption\Decryption Process
|
|
|
Unique bit sequences that algorithms rely on.
|
Encryption Keys
|
|
|
Should be hard to determine (long, random, and changed periodically)
|
Encryption Keys
|
|
|
Should be kept secret at all times
|
Encryption Keys
|
|
|
_____ algorithms use the same key for encryption and decryption
|
Symmetric
|
|
|
_____ algorithms use different keys for encryption and decryption
|
Asymmetric
|
|
|
public/private key cryptography
|
Asymmetric Algorithms
|
|
|
_____ _____ are easy to obtain and create a detectable pattern that makes breaking the encryption easy – should be avoided as much as possible
|
Weak keys
|
|
|
Act of deliberately accessing computer systems and networks without authorization
|
Hacking
|
|
|
Act of exceeding the ones authority in a system
|
Hacking
|
|
|
Implies preparation and persistent multiple attempts when searching for an unpatched system’s vulnerability
|
Hacking
|
|
|
Implies several common categories – unstructured, structured, and highly-structured threats
|
Hacking
|
|
|
May involve a variety of levels of technical expertise
|
Hacking
|
|
|
Individual attackers only – insiders or outsiders
|
Unstructured Hacking Threats
|
|
|
Attack for a short time only (months as the longest)
|
Unstructured Hacking Threats
|
|
|
Have little financial backing
|
Unstructured Hacking Threats
|
|
|
Have low level of technical expertise – download and run software created by others (can’t create a code)
|
Script Kiddies
|
|
|
Don’t attack specific targets – search for targets where a particular vulnerability is not patched
|
Script Kiddies
|
|
|
Fastest growing group (89% of malicious activity)
|
Script Kiddies
|
|
|
Possess significant technical expertise – are able to create a code
|
Hackers
|
|
|
Known for attacking a wide variety of targets
|
Hackers
|
|
|
Responsible for about 9% of malicious online activity
|
Hackers
|
|
|
Possess exceptional technical expertise – able to find new vulnerabilities and create tools used for attacks
|
Elite Hackers
|
|
|
Responsible for about 2% of malicious online activity
|
Elite Hackers
|
|
|
Represented by criminal organizations – target large amounts of money transferred over online systems
|
Structured Threats
|
|
|
Imply more planning, better financial backing, longer attacks, and collusion with insiders
|
Structured Threats
|
|
|
Responsible for fraud, extortions, thefts, forgeries, embezzlements, etc.
|
Structured Threats
|
|
|
Represented by large groups of people – separatist groups, terrorist organizations, and nations
|
Highly Structured Threats
|
|
|
Common goal – to affect another nation’s critical infrastructures (water, electricity, oil/gas refineries, finance, communications)
|
Highly Structured Threats
|
|
|
Imply years of preparation, large attacker groups, vast financial backing, and rely on insiders and spies
|
Highly Structured Threats
|
|
|
Use information warfare as the mean – commonly target information and processing equipment
|
Highly Structured Threats
|
|
|
May also use information as a weapon
|
Highly Structured Threats
|
|
|
The unconstrained medium leads to potential security issues
|
major disadvantage of wireless
|
|
|
Wireless signal can be intercepted by an attacker – can run encryption breaking, denial-of-service, etc. attacks
|
Disadvantage of Wireless
|
|
|
The original IEEE 802.11 standard implied few weak security features – addressed basic access control, encryption, and authentication
|
Disadvantage of Wireless
|
|
|
Intended to guard the availability of information – only allows authorized traffic and connections to an AP
|
Access Control
|
|
|
Defined as Layer 2 filtering by the IEEE standard – restricts access to the WLAN at the MAC layer
|
Access Control
|
|
|
Commonly implemented as MAC address filtering – using 48-bit addresses in the source address field
|
Access Control
|
|
|
Can be implemented permissive or restrictive way – commonly depending on the security policy
|
Access Control
|
|
|
_____ filtering implies manually entering unauthorized MAC addresses into the AP – all other devices would be allowed to the network
|
Permissive
|
|
|
_____ filtering implies manually entering authorized MAC addresses into the AP – all other devices would not be allowed to the network
|
Restrictive
|
|
|
Requires wireless clients to supply security credentials prior to associating with a wireless network
|
Authentication
|
|
|
Leads to granting or denying access to the new device
|
Authentication
|
|
|
Two basic types – Open System and Shared Key
|
Authentication
|
|
|
Wireless clients scan for beacon frames from access points – retrieve SSID of the wireless network
|
Authentication, Open System (“SSID Filtering”)
|
|
|
Clients include the SSID of the network to be joined into association request frames they send to the AP
|
Authentication, Open System (“SSID Filtering”)
|
|
|
The AP compares the SSID received to the one it uses and authenticates the client device in case of a match
|
Authentication, Open System (“SSID Filtering”)
|
|
|
The AP responds with the association response frame – contains an acceptance/rejection notice
|
Authentication, Open System (“SSID Filtering”)
|
|
|
Default on most access points – used for simplicity
|
Authentication, Open System (“SSID Filtering”)
|
|
|
Implies the AP sending a block of clear text (challenge) to the wireless client that requests to join the network
|
Shared Key Authentication
|
|
|
The client encrypts the challenge with a preconfigured WEP key and sends the resultant cipher to the AP
|
Shared Key Authentication
|
|
|
The AP decrypts the cipher and compares the plaintext to the original challenge sent – authenticates the client in case the two strings match
|
Shared Key Authentication
|
|
|
WEP encryption is used rarely today – modern devices use other algorithms or hashing functions
|
Shared Key Authentication
|
|
|
Optional – devices use Open System one by default
|
Shared Key Authentication
|
|
|
Encryption algorithms must work well when implemented both in hardware and software
|
Efficient
|
|
|
Secret keys used should be long and random, and must be changed periodically
|
Reasonably Strong
|
|
|
Packet-level encryption is needed
|
Self-synchronizing
|
|
|
Must meet the guidelines set by the US Department of Commerce to be exported overseas
|
Exportable
|
|
|
The implementation shouldn’t be enforced
|
Optional
|
|
|
WLAN Cryptography Objectives include being _____, Reasonably strong, Self-synchronizing, Exportable, and Optional.
|
Efficient
|
|
|
WLAN Cryptography Objectives include being Efficient, _____ _____, Self-synchronizing, Exportable, and Optional.
|
Reasonably strong
|
|
|
WLAN Cryptography Objectives include being Efficient, Reasonably strong, _____-_____, Exportable, and Optional.
|
Self-synchronizing
|
|
|
WLAN Cryptography Objectives include being Efficient, Reasonably strong, Self-synchronizing, _____, and Optional.
|
Exportable
|
|
|
WLAN Cryptography Objectives include being Efficient, Reasonably strong, Self-synchronizing, Exportable, and _____.
|
Optional
|
|
|
Described within the original IEEE 802.11 standard
|
Wired Equivalent Privacy (WEP) Encryption
|
|
|
Relies on a single secret key used on both client and the AP at a time – a symmetric encryption algorithm
|
Wired Equivalent Privacy (WEP) Encryption
|
|
|
Uses keys of a minimum length of 40 bits – with vendors adding an option to use longer 104-bit keys
|
Wired Equivalent Privacy (WEP) Encryption
|
|
|
Employs the RC4 encryption algorithm, pseudo-random numbers, single XOR logical operation – not strong
|
Wired Equivalent Privacy (WEP) Encryption
|
|
|
Nowadays, both 40 and 104-bit keys are considered weak and can provide limited security of data only
|
Wired Equivalent Privacy (WEP) Encryption
|
|
|
Five options exist – carry different strength and format
|
WEP Encryption, Key Options
|
|
|
Under the Key Options of WEP Encryption, a 40-bit key created by entering _ ASCII characters
|
5
|
|
|
Under the Key Options of WEP Encryption, 40-bit key created by entering __ hex characters
|
10
|
|
|
Under the Key Options of WEP Encryption, 104-bit key created by entering __ASCII characters
|
13
|
|
|
Under the Key Options of WEP Encryption, 104-bit key created by entering __hex characters
|
26
|
|
|
Under the Key Options of WEP Encryption, A hexadecimal ______ consisting of 16 ACSII characters entered – used to generate encryption keys
|
passphrase
|
|
|
Under the Key Options of WEP Encryption, A hexadecimal passphrase consisting of __ ACSII characters entered – used to generate encryption keys
|
16
|
|
|
An incompatibility issue exists between vendors that discourages use of _____– different keys may be generated from the same sequence of 16 characters
|
passphrases
|
|
|
Wireless devices hold up to _____ WEP keys at once – different keys may be used to encrypt traffic at various locations (work, home, etc)
|
four
|
|
|
Wireless devices hold up to four WEP keys at once – _____ keys may be used to encrypt traffic at various locations (work, home, etc)
|
different
|
|
|
One of the keys is designated as _____ key and used for encrypting data – may be different on both ends
|
default
|
|
|
MAC frames carry a _-bit field that identifies the index of the key that’s being used – data will be decrypted with the key that matches the one used for encryption
|
2
|
|
|
MAC frames carry a 2-bit field that identifies the _____ of the key that’s being used – data will be decrypted with the key that matches the one used for encryption
|
index
|
|
|
___ frames carry a 2-bit field that identifies the index of the key that’s being used – data will be decrypted with the key that matches the one used for encryption
|
MAC
|
|
|
The keys and their order must be _____ on the access point and the wireless clients
|
same
|
|
|
Changing default key on the _____ device requires no changes on the access point – simplifies administration
|
client
|
|
|
Using different WEP keys per client is used to ______ security greatly – rarely used nowadays
|
increase
|
|
|
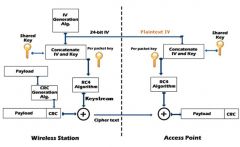
The shared secret key is concatenated by a __-bit initialization vector (IV) – value that increments every time a packet is encrypted
|
24
|
|
|
The shared secret key is concatenated by a 24-bit _____ _____ – value that increments every time a packet is encrypted
|
initialization vector (IV)
|
|
|
– an integrity check value (ICV) – is calculated via cyclic redundancy check (CRC) and appended to the end of the message
|
A checksum
|
|
|
A checksum – an _____ _____ _____ – is calculated via cyclic redundancy check (CRC) and appended to the end of the message
|
integrity check value (ICV)
|
|
|
A checksum – an integrity check value (ICV) – is calculated via _____ _____ _____ and appended to the end of the message
|
cyclic redundancy check (CRC)
|
|
|
A checksum – an integrity check value (ICV) – is calculated via cyclic redundancy check (CRC) and appended to the _____of the message
|
end
|
|
|
The _____ / _____ pair is fed into RC4 stream cipher that generates a random bit sequence (“keystream”) that’s equal in length to the text plus the ICV
|
shared key/IV
|
|
|
The shared key/IV pair is fed into _____ stream cipher that generates a random bit sequence (“keystream”) that’s equal in length to the text plus the ICV
|
RC4
|
|
|
The shared key/IV pair is fed into RC4 stream cipher that generates a _____ _____ _____ (“keystream”) that’s equal in length to the text plus the ICV
|
random bit sequence
|
|
|
The shared key/IV pair is fed into RC4 stream cipher that generates a random bit sequence (“keystream”) that’s equal in _____ to the text plus the ICV
|
length
|
|
|
The ciphertext is created by bit-by-bit _____ the text plus ICV and the keystream
|
XORing
|
|
|
The ciphertext is created by bit-by-bit XORing the text plus _____ and the keystream
|
ICV
|
|
|
The ciphertext is created by bit-by-bit XORing the text plus ICV and the _____
|
keystream
|
|
|
The IV is added to the _____ of the ciphertext and the encrypted data is ready for transmission
|
front
|
|
|
The _____ separates the IV from the ciphertext and by combines the IV with the appropriate secret key
|
receiver
|
|
|
The receiver separates the __ from the ciphertext and by combines the IV with the appropriate secret key
|
IV
|
|
|
The receiver separates the IV from the _____ and by combines the IV with the appropriate secret key
|
ciphertext
|
|
|
The receiver separates the IV from the ciphertext and by combines the __ with the appropriate secret key
|
IV
|
|
|
The receiver separates the IV from the ciphertext and by combines the IV with the appropriate _____ _____
|
secret key
|
|
|
___ algorithm generates a keystream
|
RC4
|
|
|
______is XORed with the ketystream – the text and the original ICV are extracted, followed by CRC check
|
Ciphertext
|
|
|
Ciphertext is _____ with the ketystream – the text and the original ICV are extracted, followed by CRC check
|
XORed
|
|
|
Ciphertext is XORed with the _____– the text and the original ICV are extracted, followed by CRC check
|
ketystream
|
|
|
Ciphertext is XORed with the ketystream – the text and the original ICV are _____, followed by CRC check
|
extracted
|
|
|
Ciphertext is XORed with the ketystream – the text and the original ICV are extracted, followed by ___ check
|
CRC
|
|
|
Requires manual management – difficult on mid-sized and large ESS networks and in case of frequent addition and removal of wireless clients
|
MAC Address Filtering
|
|
|
Subject to human errors – lead to denial of connection to legitimate clients and may open potential venues for a variety of attacks
|
MAC Address Filtering
|
|
|
MAC addresses are easy to capture using sniffers, through reassociation, or by breaking physical security
|
MAC Address Filtering
|
|
|
Once captured, they can be used for joining the network
|
MAC Address Filtering
|
|
|
Numerous software tools implement MAC spoofing – allows changing the MAC address in software
|
MAC Address Filtering
|
|
|
Some NICs allow for a substitute physical address to be used – spoofed MAC addresses can be presented
|
MAC Address Filtering
|
|
|
Because of its vulnerabilities and lack of flexibility, _____ _____ _____ can’t be used within enterprise
|
MAC address filtering
|
|
|
Based on matching SSID only – easy to discover
|
Open System Authentication
|
|
|
With Open System Authentication, SSID can be found on the device that is already authenticated – as result of a _____ security breach
|
physical
|
|
|
With Open System Authentication, by default, SSID is broadcasted by access points within ______ frames they send – can be captured by sniffers
|
beacon
|
|
|
With Open System Authentication, some access points can be configured to prevent including the SSID into beacon frames – may prevent _____ devices from freely roaming between them
|
legitimate
|
|
|
With Open System Authentication, _____ SSIDs are well-known and published – may not be changed by administrators timely
|
default
|
|
|
With Open System Authentication, the SSID is transmitted in _____ during the initial negotiation – easy to capture using sniffers
|
plaintext
|
|
|
With Open System Authentication, an attacker can also force negotiation by sending a forged _____ frame to a wireless device – will attempt to reconnect to the AP exposing SSID
|
disassociation
|
|
|
With Open System Authentication, The SSID can be captured from the _____– multiple wireless tools are freely available online
|
negotiation
|
|
|
Use of Open System authentication is _____ when security is a concern
|
discouraged
|
|
|
With Shared Key Authentication, An attacker only needs to know one ____ – can be captured via physical access to device or through shoulder surfing
|
key
|
|
|
With Shared Key Authentication, The access point sends a _____ in plaintext – vulnerable to interception
|
challenge
|
|
|
With Shared Key Authentication, Both the challenge and the client’s response can be captured – then the key that was used for ______ can be derived
|
encryption
|
|
|
With Shared Key Authentication, An attacker can try to derive the key by running a _____ _____ or a dictionary attack against the message
|
brute force
|
|
|
With Shared Key Authentication, An attacker can try to derive the key by running a brute force or a _____ attack against the message
|
dictionary
|
|
|
With Shared Key Authentication, The key must be configured on every device – difficult within an ___ environment
|
ESS
|
|
|
With Shared Key Authentication, Inherits additional vulnerabilities in case ___ keys are used – they are short and not truly random
|
WEP
|
|
|
Both authentication types (Open and Shared Key) provided within the _____ _____ standard are not secure – strong authentication is achieved by using digital certificated only
|
IEEE 802.11
|
|
|
In brute force attack, An attacker tries decrypting the message with every possible key – generated by changing one ___ at a time
|
bit
|
|
|
A _____-_____ attack is effective for short keys, infeasible for longer ones.
|
brute-force
|
|
|
In a _____ attack, an attacker Takes each word from a predefined dictionary and encodes it same way the passphrase is encoded
|
dictionary
|
|
|
In a dictionary attack, Attacker compares the encoded dictionary words against those in the encrypted _____
|
frame
|
|
|
_____ may be used for generating WEP leys – not too secure and not recommended
|
Passphrases
|
|
|
Uses 24-bit IV and 40- or 104-bit secret key – result in a 64- or 128-bit encryption key – short and nonsecure
|
WEP Encryption
|
|
|
WEP Encryption Transmits IV in _____– makes the effective secret part of encryption keys only 40 or 104 bit long
|
plaintext
|
|
|
WEP Encryption Repeats IV every 16,777,216 times – a busy AP sending and receiving ~ 900 packets each second would repeat the IV every _____ hours
|
five
|
|
|
Some wireless systems always start with the same IV after the system is _____ and then follow the same sequence of incrementing IVs – easy to capture
|
restarted
|
|
|
It has been proven that several IVs – weak IVs – can reveal key bytes after _____ _____
|
statistical analysis
|
|
|
As result, WEP keys of either 40- or 128-bit key length can be derived after as few as _ _____ frames– takes around four hours on a high-usage WLAN
|
4 million
|
|
|
RC4 uses a pseudo-random number generator to create the keystream – no _____ _____ numbers
|
true random
|
|
|
___ isn’t the most effective security algorithm
|
RC4
|
|
|
_____ algorithm is not the strongest one for integrity
|
CRC
|
|
|
Subject to IV replay, key stream, bit-flipping, and other attacks – with freeware tools widely available online
|
WEP Encryption
|
|
|
A number of secure authentication technologies is available – _____\_____ solutions can be used for authenticating wireless users
|
RADIUS/DIAMETER
|
|
|
WEP is lightweight and compatible with older devices –same hardware can be used for stronger _____
|
encryption
|
|
|
_____ WEP keys can be used instead of static ones
|
Dynamic
|
|
|
___ may be replaced by a stronger hashing function
|
CRC
|
|
|
An attacker floods the RF spectrum with noise that represents itself as valid traffic being transmitted
|
DoS Jamming
|
|
|
All wireless devices sense the medium before transmitting (CSMA/CA) – see the channel as busy and none of them attempts transmitting
|
DoS Jamming
|
|
|
An attacker sends a series of disassociation frames to the client – forces it to repeatedly disassociate and reassociate with the AP
|
DoS Reassociation
|
|
|
This kind of attack disables transmission of the actual data
|
DoS Reassociation
|
|
|
Makes it seem that two parties are communicating with each other directly – with a third party actually intercepting, sending and receiving data between them
|
Man-in-the-Middle (“TCP/IP Hijacking”)
|
|
|
In a _____ Man-in-the-Middle (“TCP/IP Hijacking”) attack, the attacker captures the data that is being transmitted and then sends it on to the original recipient without his presence being detected
|
Passive
|
|
|
In a _____ Man-in-the-Middle (“TCP/IP Hijacking”) attack, the attacker captures the data that is being transmitted and alters them before sending them on
|
Active
|
|
|
Implemented by attackers setting up their own AP and tricking wireless devices to communicate to it
|
Man-in-the-Middle (“TCP/IP Hijacking”)
|
|
|
In a SYN Flood DoS, it Exploits the OSI _____ layer vulnerabilities
|
Transport
|
|
|
In a SYN Flood DoS, Upon receiving a client’s SYN request, the server responds with an ___
|
ACK
|
|
|
In a SYN Flood DoS, The server waits for the client’s final reply – keeps the connection open with _____ reserved for it
|
memory
|
|
|
In a SYN Flood DoS, Attackers make servers unavailable by flooding them with SYN requests – while final replies _____ arrive
|
never
|
|
|
In a SYN Flood DoS, Waiting for too many replies _____ the server’s resources, making it nonfunctional and unavailable for legitimate requests for service
|
exhausts
|
|
|
Confidentiality through strong encryption and secure authentication are required on a WLAN – the original _____ _____ standard didn’t offer a good solution
|
IEEE 802.11
|
|
|
The same group tried addressing WEP problems via two intermediate solutions – _____ and _____ _____
|
WEP2 and Dynamic WEP
|
|
|
Two comprehensive solutions – ______ and _____ – were developed by the IEEE and the Wi-Fi Alliance, correspondingly
|
802.11i and Wi-Fi Protected Access (WPA)
|
|
|
Two comprehensive solutions – 802.11i and Wi-Fi Protected Access (WPA) – were developed by the _____ and _____, correspondingly
|
IEEE and the Wi-Fi Alliance
|
|
|
Developed by the same IEEE Task Group i (TGi) that developed the original WEP
|
WEP2
|
|
|
Offers two security enhancements – longer keys and support for Kerberos authentication
|
WEP2
|
|
|
Naturally extends key+IV space to 128-bits – used to be much more secure than using 64-bit keys
|
WEP2
|
|
|
Enabled wireless clients to use encrypted tickets issued by secure Kerberos server for identity verification
|
WEP2
|
|
|
The tickets would carry client data clients – identify, allowed actions, etc – would expire after several hours
|
WEP2
|
|
|
Doesn’t prevent collisions – makes identification of two packets derived from the same IV possible
|
WEP2, Disadvantages
|
|
|
Still uses lightweight but not secure RC4 algorithm
|
WEP2, Disadvantages
|
|
|
Inherits disadvantages of Kerberos – single point of failure, clock synchronization, vulnerability to dictionary attacks, etc.
|
WEP2, Disadvantages
|
|
|
Not much more secure than the original WEP – was not widely adopted as replacement for WEP
|
WEP2, Disadvantages
|
|
|
Solves the weak IV problem by rotating the keys frequently – makes cracking more difficult
|
Dynamic WEP
|
|
|
Uses different keys for unicast and broadcast traffic – broadcast keys are same for all users on the particular subnet and the access point
|
Dynamic WEP
|
|
|
Unicast keys are unique for each user session, generated dynamically, and changed when the user roams to a new AP, or logs out and logs back in
|
Dynamic WEP
|
|
|
Doesn’t protect against man-in-the-middle and DoS attacks – was quickly replaced by better solutions
|
Dynamic WEP
|
|
|
Developed by a group that originated from the IEEE TGi task group that was disbanded
|
IEEE 802.11i
|
|
|
Provides solid wireless security model – addresses both secure encryption and authentication
|
IEEE 802.11i
|
|
|
Includes multiple new features such as key caching, pre-authentication, etc.
|
IEEE 802.11i
|
|
|
Also known as the Robust Security Network (RSN)
|
IEEE 802.11i
|
|
|
A new standing IEEE committee ensures that new additions to the 802.11 standard don’t carry their own security issues
|
IEEE 802.11i
|
|
|
The RC4 stream cipher is replaced by the _____ _____ _____ algorithm (block cipher)
|
Advanced Encryption Standard (AES)
|
|
|
AES replaced ___ and is considered secure for many years to come – US government encryption standard
|
DES
|
|
|
Plaintext is divided into ___-bit blocks – with entire block encrypted at a time via multiple rounds
|
128
|
|
|
___ supports 128-, 192-, and 256-bit long keys – with 10, 12, or 14 encryption rounds used, respectively
|
AES
|
|
|
Longer keys and higher number or rounds affect the overall _____ of the system that uses AES
|
performance
|
|
|
___is computationally heavy – mobile devices require hardware implementation on a dedicated chip for better performance
|
AES
|
|
|
Wireless Authentication was accomplished according to the _____ _____ standard – originally developed for wired networks (supported by Windows 2000 SP4 or later OS)
|
IEEE 802.1x
|
|
|
Implements port security – all network traffic to mobile clients that try accessing the network is blocked until their identities are verified by an authentication server
|
IEEE 802.1x Authentication
|
|
|
802.1x authenticates in the _____only – session may be vulnerable to a man-in-the-middle attack
|
beginning
|
|
|
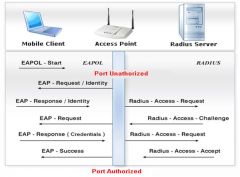
A wireless client contacts the AP with a request to join the WLAN – the communication port is put to the unauthorized state (i.e. only 802.1x traffic is allowed)
|
802.11i Authentication Process
|
|
|
The AP requests the new device to verify its identity – the client sends identity information to the AP
|
802.11i Authentication Process
|
|
|
The AP passes identity data onto an authentication server – secured by digital certificates and encryption
|
802.11i Authentication Process
|
|
|
The authentication server verifies the client’s identity – notifies the access point about its decision
|
802.11i Authentication Process
|
|
|
The client joins the network if authenticated only
|
802.11i Authentication Process
|
|
|
The port is set to unauthorized state upon logoff again
|
802.11i Authentication Process
|
|
|
The Extensible Authentication Protocol over LANs (EAPOL) is used between the client and the AP
|
802.11i Authentication Process
|
|
|
The communication between the access point and the authentication server is ruled by appropriate protocol (RADIUS or DIAMETER)
|
802.11i Authentication Process
|
|
|
Requires a Public Key Infrastructure (PKI) to operate
|
802.11i Authentication Process
|
|
|
In the 802.11i standard, _____ _____ Enables caching clients’ credentials on the network to avoid retransmitting them in case a client roams away from the AP and later returns
|
Key Caching
|
|
|
In the 802.11i standard, _____ _____ makes roaming between APs faster by allowing mobile clients to authenticate to the new AP before moving to it
|
Pre-Authentication
|
|
|
In the 802.11i standard, the device would send a _____-_____ packet that is routed to the remote AP – through the AP the device is currently authenticated with
|
pre-authentication
|
|
|
Created as an intermediate measure while the IEEE 802.11i standard was under development
|
Wi-Fi Protected Access (WPA)
|
|
|
A MAC layer subset of the 802.11i standard – addresses both encryption and authentication
|
Wi-Fi Protected Access (WPA)
|
|
|
Replaces original WEP by stronger Temporary Key Integrity Protocol (TKIP) encryption
|
Wi-Fi Protected Access (WPA)
|
|
|
Allows using either IEEE 802.1x protocol or pre-shared key (PSK) for authentication of wireless clients
|
Wi-Fi Protected Access (WPA)
|
|
|
Encryption solution – much stronger than WEP
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
After accepting a device’s credentials, the authentication server uses 802.1x to produce a unique master key for that user session
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
Within the Temporary Key Integrity Protocol (TKIP), The _____ key is distributed to the client and the AP
|
master
|
|
|
Substitutes this temporary key for the WEP base key and constructs a new 128-bit key for every packet – these have limited lifetimes and are replaced frequently
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
Optional in standard WLAN, required in WPA
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
MIC provides better protection against forgeries
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
Replaces the CRC function used by WEP – complicates capturing and altering, and then resending data
|
Message Integrity Check (MIC) Function
|
|
|
CRC is not strong enough – vulnerable to modification of both the message and the CRC field
|
Message Integrity Check (MIC) Function
|
|
|
MIC function is much stronger than CRC
|
Message Integrity Check (MIC) Function
|
|
|
Offers an optional countermeasure – if a MIC error occurs, clients are disassociated, with new associations prevented for one minute
|
Message Integrity Check (MIC) Function
|
|
|
Used within TKIP encryption
|
Message Integrity Check (MIC) Function
|
|
|
Dynamically generated keys significantly increase time between consequent possible collisions – ensure that a valid packet isn’t recorded and then retransmitted
|
Temporary Key Integrity Protocol (TKIP)
|
|
|
Temporary Key Integrity Protocol (TKIP) Increases the size of the IV to __ bits and uses it as a sequence number for each packet
|
48
|
|
|
Both transmitter and receiver initialize the packet sequence to zero whenever new _____ keys are set
|
TKIP
|
|
|
Works on the same hardware as WEP – older clients and APs may require software or firmware upgrades
|
Temporary Key Integrity Protocol
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The device starts with having two keys – a 128-bit encryption _____ key and a 64-bit Message Integrity Check (MIC) key value
|
temporal
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The device starts with having two keys – a 128-bit encryption temporal key and a 64-bit _____ _____ _____ key value
|
Message Integrity Check (MIC)
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The temporal key is XORed with the sender’s ___ address to create an Intermediate Value I
|
MAC
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The temporal key is XORed with the sender’s MAC address to create an Intermediate Value _
|
I
|
|
|
Within Temporary Key Integrity Protocol, Encryption, Intermediate Value I is mixed with a _____ number (former IV field in WEP) to produce Intermediate Value II – entered into the PRNG
|
sequence
|
|
|
Within Temporary Key Integrity Protocol, Encryption, Intermediate Value I is mixed with a sequence number (former IV field in WEP) to produce Intermediate Value __ – entered into the PRNG
|
II
|
|
|
Within Temporary Key Integrity Protocol, Encryption, Intermediate Value I is mixed with a sequence number (former IV field in WEP) to produce Intermediate Value II – entered into the _____
|
PRNG
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The random number generator generates a _____
|
keystream
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The MIC key and the sender’s and receiver’s MAC addresses are all run through a ___function – a new MIC value obtained
|
MIC
|
|
|
Within Temporary Key Integrity Protocol, Encryption, The ciphertext is obtained via _____ the keystream and the plaintext message with the MIC value appended to it bit-by-bit
|
XORing
|
|
|
Wi-Fi Protected Access (WPA) Authentication is accomplished by using either _____ _____ protocol or pre-shared key (PSK) technology
|
IEEE 802.1x
|
|
|
Wi-Fi Protected Access (WPA) Authentication is accomplished by using either IEEE 802.1x protocol or _____ _____ technology
|
pre-shared key (PSK)
|
|
|
_____authentication uses a passphrase as a seed to generate the encryption key – has to be entered manually on each device
|
PSK
|
|
|
PSK authentication uses a passphrase as a seed to generate the encryption key – has to be entered _____ on each device
|
manually
|
|
|
Implementation of IEEE 802.1x protocol is too complex for _____ wireless networks – enterprises only
|
SOHO
|
|
|
PSK is vulnerable to possible decryption of _____ _____ and insertion of fake packets – this problem is fixed in AES-based WPA2
|
short packets (ARP)
|
|
|
PSK is vulnerable to possible decryption of short packets (ARP) and insertion of _____ packets – this problem is fixed in AES-based WPA2
|
fake
|
|
|
Based on the final IEEE 802.11i standard – allows both AES and TKIP clients to operate on the same WLAN
|
WPA2
|
|
|
More secure than WPA – allows using AES encryption
|
WPA2
|
|
|
More flexible than 802.11i – allows using AES or TKIP
|
WPA2
|
|
|
Supports IEEE 802.1x and PSK authentication
|
WPA2
|
|
|
Most popular solution for SOHO wireless networks
|
WPA2
|
|
|
Implies using currently installed or inexpensive new equipment temporarily – until equipment that supports better security features can be implemented
|
Transitional Security Model
|
|
|
Used when better security models aren’t feasible for financial or organizational reasons – with a plan to purchase and install better equipment in future
|
Transitional Security Model
|
|
|
Should be considered as temporary solution only – with best available authentication and encryption configured
|
Transitional Security Model
|
|
|
Users must be aware of weak spots of implementation
|
Transitional Security Model
|
|
|
easy to implement and supported by all 802.11 access points
|
Shared key authentication
|
|
|
fast and supported by all 802.11 access points (longest keys should be used, passphrase use is not recommended since weak keys are created)
|
WEP encryption
|
|
|
broadly supported (disabled by default, should be used restrictive way, not suitable for frequent changes in wireless client base)
|
MAC filtering
|
|
|
broadly supported (enabled by default, not suitable for many roaming clients)
|
Disable SSID broadcast
|
|
|
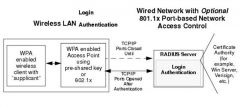
Suitable for SOHO wireless networks with up to 10 users and no secure authentication server available
|
Personal Security Model
|
|
|
Implies using PSK authentication
|
Personal Security Model
|
|
|
Relies on WPA for encryption – with older devices using WPA (TKIP) and newer ones using WPA2 (AES)
|
Personal Security Model
|
|
|
Assumes implementation of the latest WPA version supported by wireless equipment
|
Personal Security Model
|
|
|
Provides intermediate level of security – but commonly much more secure than transitional model
|
Personal Security Model
|
|
|
With Personal Authentication, A passphrase that’s manually entered on the _____ is used as a starting seed value for encryption key generation
|
AP
|
|
|
With Personal Authentication, The passphrase can be between _ and __ characters – with special characters and spaces allowed
|
8 and 63
|
|
|
With Personal Authentication, Passphrases of at least __ ASCII characters or at least __ hex digits are recommended
|
20\24
|
|
|
In Personal Security Model Authentication, Implements the _____ feature – security keys are automatically changed after a set number of packets (rekey interval) is sent
|
rekeying
|
|
|
In Personal Security Model Authentication, Implements the rekeying feature – security keys are automatically changed after a set number of packets _____ _____ is sent
|
(rekey interval)
|
|
|
Within the Personal Security Model Encryption,_____ _____ uses TKIP thus compatible with existing WEP infrastructure (more secure than WEP)
|
WPA-based Encryption
|
|
|
Within the Personal Security Model Encryption, _____ _____ allows using both TKIP and AES thus provides maximum flexibility
|
WPA2-based Encryption
|
|
|
Suitable for mid-sized and large organizations – implies that a secure authentication server is available
|
Enterprise Security Model
|
|
|
Implies connections to a RADIUS (DIAMETER) server via the IEEE 802.1x authentication protocol
|
Enterprise Security Model
|
|
|
Relies on WPA for encryption – with older devices using WPA (TKIP) and newer ones using WPA2 (AES)
|
Enterprise Security Model
|
|
|
Assumes implementation of the latest WPA version supported by wireless equipment
|
Enterprise Security Model
|
|
|
Provides the highest level of security of all models
|
Enterprise Security Model
|
|
|
WPA Authentication =
|
PSK or 802.1x
|
|
|
WPA Encryption =
|
TKIP
|
|
|
WPA Encryption Hardware =
|
WEP
|
|
|
WPA Complexity =
|
Lowest
|
|
|
WPA2 Authentication =
|
PSK or 802.1x
|
|
|
WPA2 Encryption =
|
TKIP or AES
|
|
|
WPA2 Encryption Hardware =
|
WEP or Special
|
|
|
WPA2 Complexity =
|
Average
|
|
|
IEEE 802.11i Authentication =
|
802.1x
|
|
|
IEEE 802.11i Encryption =
|
AES
|
|
|
IEEE 802.11i Encryption Hardware =
|
Special
|
|
|
IEEE 802.11i complexity =
|
Highest
|
|
|
Transitional Security Model Authentication =
|
Best Available
|
|
|
Transitional Security Model Based on Solution =
|
Basic Features
|
|
|
Transitional Security Model Protection =
|
Minimal
|
|
|
Transitional Security Model Usability =
|
Temporary
|
|
|
Personal Security Model Authentication =
|
PSK
|
|
|
Personal Security Model Based on Solution =
|
WPA or WPA2
|
|
|
Personal Security Model Protection =
|
Good
|
|
|
Personal Security Model Usability
|
SOHO
|
|
|
Enterprise Security Model Authentication =
|
802.1x
|
|
|
Enterprise Security Model Based on Solution =
|
WPA or WPA2
|
|
|
Enterprise Security Model Protection =
|
Best
|
|
|
Enterprise Security Model USability
|
Large Networks
|
|
|
Allow connect wireless users to secure corporate networks via secure data transmission channels – tunnels – through public networks
|
Virtual Private Networks (VPN)
|
|
|
Imply configuring the two endpoints of the tunnel – each one may include a software, a firewall, or a hardware VPN concentrator
|
Virtual Private Networks (VPN)
|
|
|
Can be based on a variety of secure protocols, such as PPTP, IPSec, SSL, etc.
|
Virtual Private Networks (VPN)
|
|
|
Does not support roaming between access points
|
Virtual Private Networks (VPN)
|
|
|
Constantly monitor the RF medium for attacks – search traffic patterns via hardware or software sensors
|
Wireless Intrusion Detection Systems (WIDS)
|
|
|
Can be passive (send an alert or produce an alarm) or active (take an action when sensing an attack)
|
Wireless Intrusion Detection Systems (WIDS)
|
|
|
Identify attacks based on a database of known traffic patterns – signatures – or on abnormal network activities (“anomaly-based IDS”)
|
Wireless Intrusion Detection Systems (WIDS)
|
|
|
Signature-based IDS are limited to detecting attacks that are in the database only while anomaly-based IDS may produce multiple false alarms
|
Wireless Intrusion Detection Systems (WIDS)
|
|
|
Using Wireless Intrusion Detection Systems, Hardware Sensors, Separate hardware devices or access points that operate in a special _____ _____
|
scan mode
|
|
|
Using Wireless Intrusion Detection Systems, hardware can detect signals from _____ access points by comparing their RF signal with the database of known APs
|
rogue
|
|
|
Wireless Intrusion Detection Systems, Software Sensors May be installed on wireless devices for acting as a “_____” of mobile sensors
|
mesh
|
|
|
Wireless Intrusion Detection Systems, Software Sensors May be installed on a _____ for detecting rogue APs that connect to the wired network
|
server
|
|
|
A Web page that wireless users are forced to visit before they are granted access of some kind
|
Captive Portal
|
|
|
Used to notify users of wireless policies and rules, to advertise products, or to authenticate users via s secure server before they are granted access
|
Captive Portal
|
|
|
Used in hotspots and other public locations – commonly takes users to a “Terms and Conditions” page
|
Captive Portal
|
|
|
802.11i Authentication
|
|

|
Open System Authentication
|
|

|
Shared Key Authentication
|
|
|
WEP Encryption
|
|
|
WPA PSK Authentication
|

